本帖最后由 x39fs0 于 2024-3-29 15:27 编辑
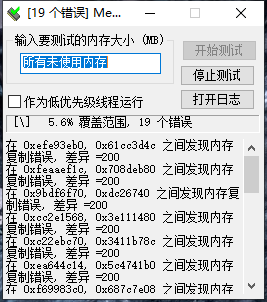
刚配的电脑,系统装的WIN10,这两天使用过程中碰到了几次蓝屏还有无故重启(重装问题还在)。
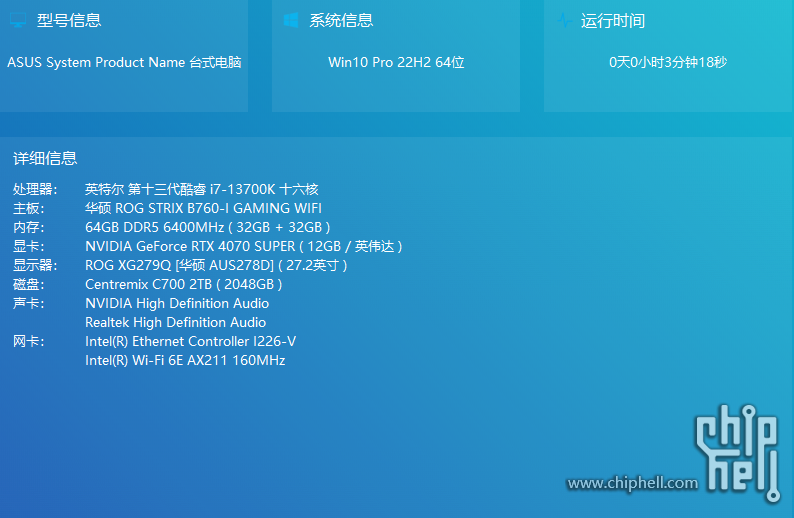
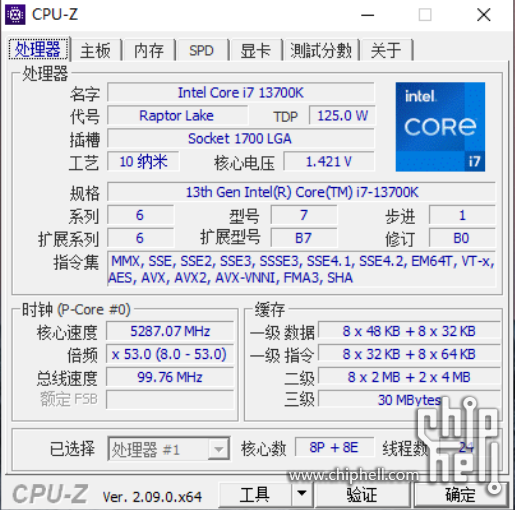
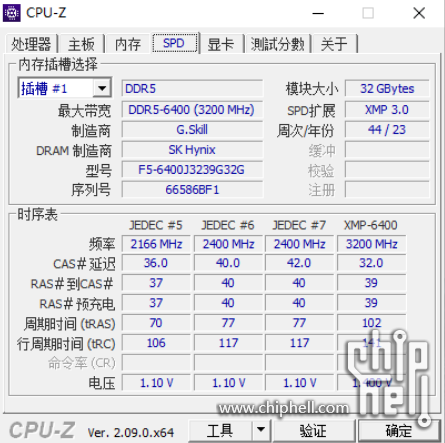
配置是13700K + B760I,内存从某鱼上捡的幻锋戟DDR5 6400 32G*2。
BIOS是最新的,只开启了XMP其它默认。
其它驱动皆为官网最新。
配置
CPUZ
CPUZ
MemTest
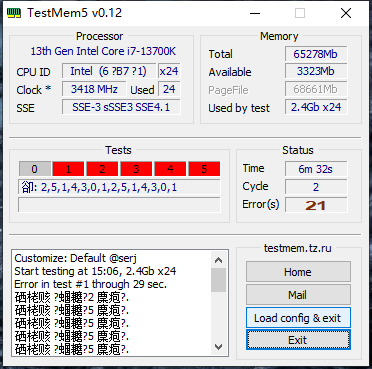
TM5
系统日志:
************* Preparing the environment for Debugger Extensions Gallery repositories **************
ExtensionRepository : Implicit
UseExperimentalFeatureForNugetShare : true
AllowNugetExeUpdate : true
NonInteractiveNuget : true
AllowNugetMSCredentialProviderInstall : true
AllowParallelInitializationOfLocalRepositories : true
EnableRedirectToV8JsProvider : false
-- Configuring repositories
----> Repository : LocalInstalled, Enabled: true
----> Repository : UserExtensions, Enabled: true
>>>>>>>>>>>>> Preparing the environment for Debugger Extensions Gallery repositories completed, duration 0.000 seconds
************* Waiting for Debugger Extensions Gallery to Initialize **************
>>>>>>>>>>>>> Waiting for Debugger Extensions Gallery to Initialize completed, duration 0.172 seconds
----> Repository : UserExtensions, Enabled: true, Packages count: 0
----> Repository : LocalInstalled, Enabled: true, Packages count: 41
Microsoft (R) Windows Debugger Version 10.0.27553.1004 AMD64
Copyright (c) Microsoft Corporation. All rights reserved.
Loading Dump File [C:\Windows\Minidump\032924-6156-01.dmp]
Mini Kernel Dump File: Only registers and stack trace are available
Symbol search path is: srv*
Executable search path is:
Windows 10 Kernel Version 19041 MP (24 procs) Free x64
Product: WinNt, suite: TerminalServer SingleUserTS
Kernel base = 0xfffff804`04000000 PsLoadedModuleList = 0xfffff804`04c2a730
Debug session time: Fri Mar 29 12:59:39.065 2024 (UTC + 8:00)
System Uptime: 0 days 1:01:02.725
Loading Kernel Symbols
...............................................................
................................................................
................................................................
....
Loading User Symbols
PEB is paged out (Peb.Ldr = 00000029`89c8a018). Type ".hh dbgerr001" for details
Loading unloaded module list
.....
For analysis of this file, run !analyze -v
nt!KeBugCheckEx:
fffff804`043fd890 48894c2408 mov qword ptr [rsp+8],rcx ss:0018:fffffa81`c0227200=000000000000000a
8: kd> !analyze -v
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
IRQL_NOT_LESS_OR_EQUAL (a)
An attempt was made to access a pageable (or completely invalid) address at an
interrupt request level (IRQL) that is too high. This is usually
caused by drivers using improper addresses.
If a kernel debugger is available get the stack backtrace.
Arguments:
Arg1: 0000438656949010, memory referenced
Arg2: 0000000000000002, IRQL
Arg3: 0000000000000000, bitfield :
bit 0 : value 0 = read operation, 1 = write operation
bit 3 : value 0 = not an execute operation, 1 = execute operation (only on chips which support this level of status)
Arg4: fffff804042839fa, address which referenced memory
Debugging Details:
------------------
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 1265
Key : Analysis.Elapsed.mSec
Value: 1293
Key : Analysis.IO.Other.Mb
Value: 0
Key : Analysis.IO.Read.Mb
Value: 0
Key : Analysis.IO.Write.Mb
Value: 0
Key : Analysis.Init.CPU.mSec
Value: 328
Key : Analysis.Init.Elapsed.mSec
Value: 35100
Key : Analysis.Memory.CommitPeak.Mb
Value: 92
Key : Bugcheck.Code.LegacyAPI
Value: 0xa
Key : Bugcheck.Code.TargetModel
Value: 0xa
Key : Dump.Attributes.AsUlong
Value: 8
Key : Dump.Attributes.KernelGeneratedTriageDump
Value: 1
Key : Failure.Bucket
Value: AV_nt!MiGetPageProtection
Key : Failure.Hash
Value: {41372a35-237d-1281-82f6-8f5f9bf6044a}
BUGCHECK_CODE: a
BUGCHECK_P1: 438656949010
BUGCHECK_P2: 2
BUGCHECK_P3: 0
BUGCHECK_P4: fffff804042839fa
FILE_IN_CAB: 032924-6156-01.dmp
DUMP_FILE_ATTRIBUTES: 0x8
Kernel Generated Triage Dump
READ_ADDRESS: fffff80404cfb390: Unable to get MiVisibleState
Unable to get NonPagedPoolStart
Unable to get NonPagedPoolEnd
Unable to get PagedPoolStart
Unable to get PagedPoolEnd
unable to get nt!MmSpecialPagesInUse
0000438656949010
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: chrome.exe
TRAP_FRAME: fffffa81c0227340 -- (.trap 0xfffffa81c0227340)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=0000438656949000 rbx=0000000000000000 rcx=0000000043865694
rdx=000870cad2932b01 rsi=0000000000000000 rdi=0000000000000000
rip=fffff804042839fa rsp=fffffa81c02274d0 rbp=000043865694995c
r8=fffffa81c0227628 r9=fffffa81c02275b8 r10=ffffbedf6fb7d7f8
r11=ffffbedf6fb7d000 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei pl nz na po nc
nt!MiGetPageProtection+0x60a:
fffff804`042839fa 488b4010 mov rax,qword ptr [rax+10h] ds:00004386`56949010=????????????????
Resetting default scope
STACK_TEXT:
fffffa81`c02271f8 fffff804`04411e29 : 00000000`0000000a 00004386`56949010 00000000`00000002 00000000`00000000 : nt!KeBugCheckEx
fffffa81`c0227200 fffff804`0440d8a3 : 00000000`00000000 00000000`00000000 ffffc108`0cbef080 00000000`00000000 : nt!KiBugCheckDispatch+0x69
fffffa81`c0227340 fffff804`042839fa : 0000007f`fffffff8 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiPageFault+0x463
fffffa81`c02274d0 fffff804`042310ee : 00000000`00000000 00000000`00000000 fffffa81`c0227628 fffffa81`c02275b8 : nt!MiGetPageProtection+0x60a
fffffa81`c0227550 fffff804`0463e52a : ffffc108`0d9cf5b0 00000000`00000000 00000000`018f0000 00000000`00000002 : nt!MiCommitExistingVad+0xcce
fffffa81`c02276a0 fffff804`0464051b : 00000000`00000000 00000000`00000000 00000000`00000000 00000029`8a5fc600 : nt!MiAllocateVirtualMemory+0x2aa
fffffa81`c0227820 fffff804`04411575 : ffffffff`ffffffff ffffc108`0cae8080 00000000`00000000 00000029`8a5fc5d8 : nt!NtAllocateVirtualMemory+0x1ab
fffffa81`c02279d0 00007fff`3b24d2e4 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiSystemServiceCopyEnd+0x25
00000029`8a5fc5b8 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : 0x00007fff`3b24d2e4
SYMBOL_NAME: nt!MiGetPageProtection+60a
MODULE_NAME: nt
IMAGE_VERSION: 10.0.19041.4170
STACK_COMMAND: .cxr; .ecxr ; kb
IMAGE_NAME: ntkrnlmp.exe
BUCKET_ID_FUNC_OFFSET: 60a
FAILURE_BUCKET_ID: AV_nt!MiGetPageProtection
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {41372a35-237d-1281-82f6-8f5f9bf6044a}
Followup: MachineOwner
--------- |
 310112100042806
310112100042806
